Cyber awareness challenge 2023 knowledge check
The purpose of the Cyber Awareness Challenge is to influence behavior, focusing on actions that authorized users can engage to mitigate threats and vulnerabilities to DoD Information Systems. This training is current, designed to be engaging, and relevant to the user.
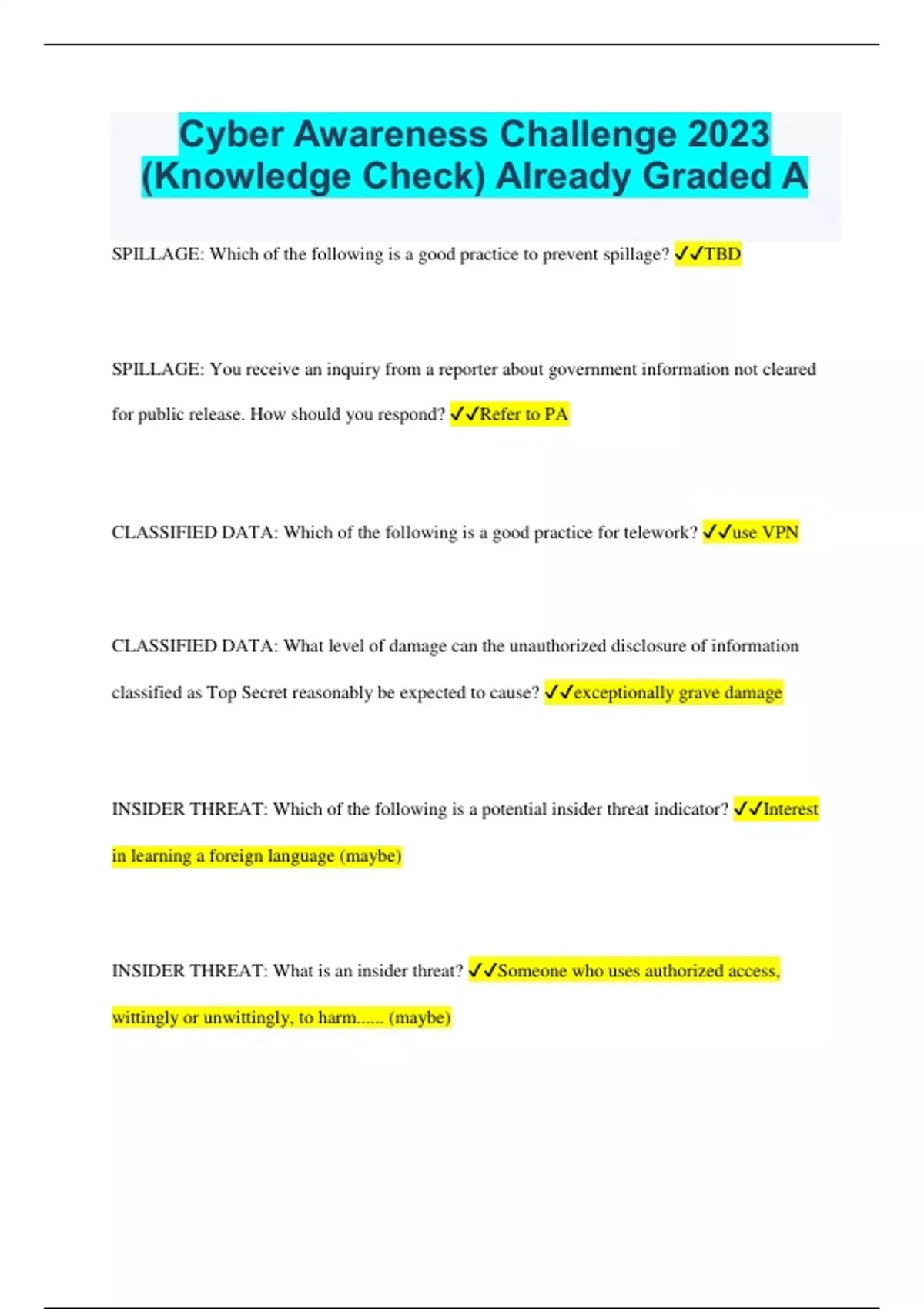
We thoroughly check each answer to a question to provide you with the most correct answers. Found a mistake? In addition to offering an overview of cybersecurity best practices, the challenge also provides awareness of potential and common cyber threats. Meeting Notes: Your meeting notes are Unclassified. This means that your notes: Answer: Do not have the potential to damage national security. What type of information does this personnel roster represent?
Cyber awareness challenge 2023 knowledge check
By using this IS which includes any device attached to this IS , you consent to the following conditions:. Acknowledgement and acceptance of the above statement is required to log in. This computer system is not authorized to process classified information. This computer system, including all related equipment, networks, and network devices including internet access is provided only for authorized U. Government use. DOD computer systems may be monitored for all lawful purposes, including to ensure their use id authorized, for management of the system, to facilitate protection against unauthorized access and to verify security procedures, survivability and operational security. Monitoring includes, but is not limited to, active attacks by authorized DOD entities to test or verify the security of this system. During monitoring, information may be examined, recorded, copied, and used for authorized purposes. All information, including personal information, placed on or sent over this system may be monitored. Use of this DOD computer system, authorized or unauthorized, constitutes consent to monitoring. Unauthorized use of this DOD computer system may subject you to criminal prosecution. Evidence of unauthorized use collected during monitoring may be used for administrative, criminal, or other adverse action. Communications using, or data stored on, this IS are not private, are subject to routine monitoring, interception, and search, and may be disclosed or used for any USG-authorized purpose.
Which best describes an insider threat? Leave a Comment Your email address will not be published.
.
Which of the following is true of removable media and portable electronic devices PEDs? Follow procedures for transferring data to and from outside agency and non-Government networks. Information improperly moved from higher to lower protection level. Which of the following is a good practice to protect classified information? Which scenario might indicate a reportable insider threat? A colleague removes sensitive information without seeking authorization. Which of the following is a reportable insider threat activity? Attempting to access sensitive information without need to know.
Cyber awareness challenge 2023 knowledge check
The purpose of the Cyber Awareness Challenge is to influence behavior, focusing on actions that authorized users can engage to mitigate threats and vulnerabilities to DoD Information Systems. This training is current, designed to be engaging, and relevant to the user. This course provides an overview of current cybersecurity threats and best practices to keep information and information systems secure at home and at work. The training also reinforces best practices to protect classified, controlled unclassified information CUI , and personally identifiable information PII. A Knowledge Check option is available for users who have successfully completed the previous version of the course. After each selection on the incident board, users are presented one or more questions derived from the previous Cyber Awareness Challenge.
What does a red dot on snapchat mean
Annabeth becomes aware that a conversation with a co-worker that involved Sensitive Compartmented Information SCI may have been overheard by someone who does not have the required clearance. Was this helpful? By using this IS which includes any device attached to this IS , you consent to the following conditions:. Each piece of content undergoes a rigorous review process to ensure accuracy, relevance, and clarity. Delete the message. This IS includes security measures e. The Quizzma Team is committed to fostering a conducive learning environment for individuals and continually strives to provide reliable and valuable educational resources on a wide array of topics. Beth taps her phone at a payment terminal to pay for a purchase. You find an unlabeled thumb drive in the parking area outside your workplace. This is not an appropriate use of GFE. Which of the following is permitted when using an unclassified laptop within a collateral classified space?
As someone who is passionate about cybersecurity, I am always on the lookout for ways to improve my knowledge and understanding of the ever-evolving digital landscape.
Privacy and Security Section Site Map. This means that your notes: Answer: Do not have the potential to damage national security. Monitoring includes, but is not limited to, active attacks by authorized DOD entities to test or verify the security of this system. Your email address will not be published. This computer system, including all related equipment, networks, and network devices including internet access is provided only for authorized U. This IS includes security measures e. PMP Practice Exam. Contact: usarmy. Which course of action should you take? You find an unlabeled thumb drive in the parking area outside your workplace. By using this IS which includes any device attached to this IS , you consent to the following conditions:. DOD computer systems may be monitored for all lawful purposes, including to ensure their use id authorized, for management of the system, to facilitate protection against unauthorized access and to verify security procedures, survivability and operational security.

As the expert, I can assist. Together we can come to a right answer.